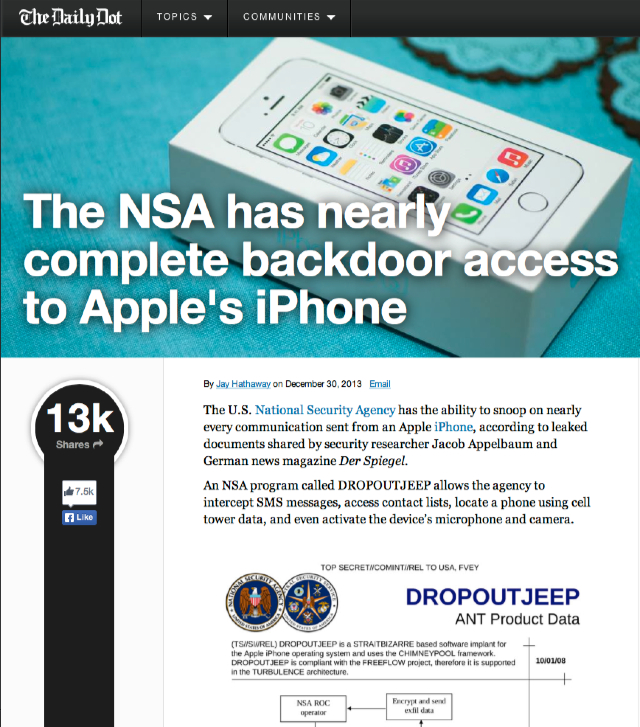
It appears the FBI’s assessment (‘assume that [your communication] will be intercepted and retained’) was based on reality … including the remote control of your phone’s microphone & camera.
According to leaked documents, the NSA claims a 100 percent success rate when it comes to implanting iOS devices with spyware. The documents suggest that the NSA needs physical access to a device to install the spyware — something the agency has achieved by rerouting shipments of devices purchased online — but a remote version of the exploit is also in the works.
From the NSA document in question: (quoted by Forbes, see: The NSA Reportedly Has Total Access To The Apple iPhone)
“DROPOUT JEEP is a software implant for the Apple iPhone that utilizes modular mission applications to provide specific SIGINT functionality. This functionality includes the ability to remotely push/pull files from the device. SMS retrieval, contact list retrieval, voicemail, geolocation, hot mic, camera capture, cell tower location, etc. Command, control and data exfiltration can occur over SMS messaging or a GPRS data connection. All communications with the implant will be covert and encrypted.”
Gawd. Alienating.
– P
Of course, I tooootally trust Android and Microsoft Windows phones … 🙂 (cough)
The NSA Has Inserted Its Code Into Android OS, Or Three Quarters Of All Smartphones and NSA Has Full “Back Door” Access To iPhone, BlackBerry And Android Smartphones, Documents Reveal Sheesh.
Update: Make of this what you will: Apple Denies Working with NSA on iPhone Backdoor
Apple has never worked with the NSA to create a backdoor in any of our products, including iPhone. Additionally, we have been unaware of this alleged NSA program targeting our products. We care deeply about our customers’ privacy and security. Our team is continuously working to make our products even more secure, and we make it easy for customers to keep their software up to date with the latest advancements. Whenever we hear about attempts to undermine Apple’s industry-leading security, we thoroughly investigate and take appropriate steps to protect our customers. We will continue to use our resources to stay ahead of malicious hackers and defend our customers from security attacks, regardless of who’s behind them.
Nice bit of FUD (Fear Uncertainty and Doubt) or is it Shock and Awe?

A couple of perspective articles…
DROPOUTJEEP. Can the NSA spy on every iPhone on the planet? GrahamCluley.com
and The NSA can do what to my iPhone? from Agilebits, Canadian makers of 1Password which includes:
Of course, if your phone, iPad or laptop was confiscated at a border for any time, like, say, this New Zealander recently (let alone Glenn Greenwald’s partner David Miranda) well, there’s ‘close access’ for you, huh?
Hard to believe this …
It beggars belief to see just how many US-based (and indeed non-US-based) tech companies appear to have actively collaborated with the NSA, allowing the NSA backdoor access to the information being stored/shared/sent on that technology.
Orwell, with his concept of ‘Big Brother’, would not have been able to even conceive of the surveillance state that exists in our Western democracies…
[…] And anyway, what do you think of the Blackphone idea? Don’t you think owning one (or having it discovered in your possessions at, say, a border control might perhaps mark you out as a ‘person of interest’? … perhaps leading to a confiscation … which, of course. gives the state security apparatus physical possession of your device, which is, cough, all they need, reportedly. […]